The evolution of blockchain came with many synonyms. There advanced many choices to the real world problems offering better business model and economic structure. The most pivotal was the evolution of Cryptocurrency. Cryptocurrency gave a new definition to the way businesses and individuals transacted. It replaced the conventional model of exchanges replacing fiat. From a regulated physical cash, there was an upspring of decentralized digital cash unbacked by a single body. While the digital cash contained many merits respective of peer-to-peer exchange, faster and cheaper transactions, it contained its own fair share of demerits. There belonged certain risks associated with cryptocurrency. One among the primary concerns was Double-Spending.
What is Double-Spending?
This refers to the incidence of an individual spending the same money twice at the same time. In other words, using the cryptocurrency more than once, creating a disparity between the spending record and the amount of that cryptocurrency available.
It is a major computing problem that every cryptocurrency should solve as it would destroy the technological grounding on which a blockchain is founded.
This article will see what double-spending is and how Bitcoin blockchain deals with it.
If you look at the issue of double-spending, it is a problem that fiat cash does not have. If you spend 10$ for a book, you cannot turn around and spend the very same 10$ anywhere else. However, a transaction with digital money has risks of double-spending associated with it.
To understand it better, let’s quickly revise how a transaction is processed in a Bitcoin Blockchain.
Here, the node that receives the transaction will send it to all the nodes in the network. They will validate the transaction by verifying the accounts addresses, balances, signatures etc. A set of valid transactions will be selected and grouped into a block. Miners try to create the blocks, and a winner will be chosen based on the Proof of Work (PoW) consensus mechanism. Blockchain will add the block from the winner node. The transaction will be considered complete, and the account balances will be updated upon the block containing the transaction details get added to the blockchain. However, this will take some time. It may vary depending on several factors.
Let’s go through a scenario.
Imagine, Alice has 5 BTC (bitcoin) in her account. She transfers that 5 BTC to Bob. Almost at the same time, Alice creates another transaction which transfers 5 BTC to Carol. So here basically Alice is trying to send the same 5 BTC to Bob and Carol.
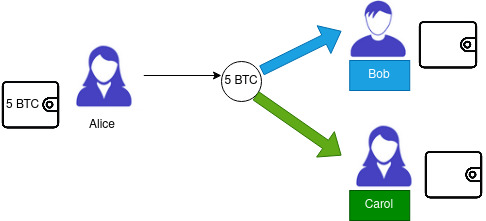
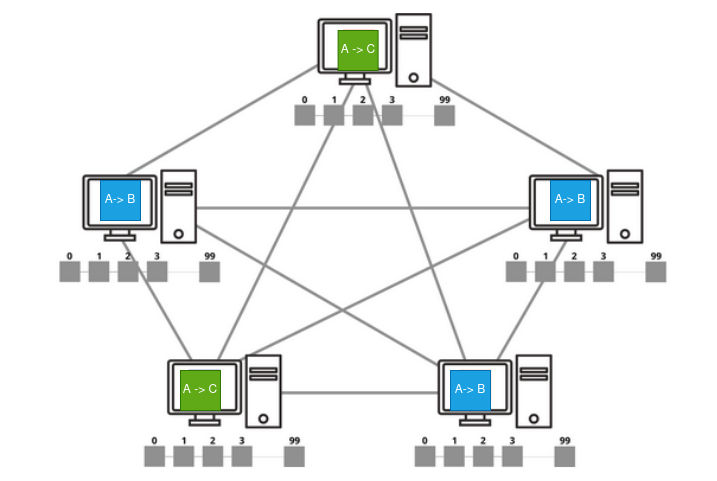
Now both the transactions will propagate through the network. Some nodes may receive Bob’s transaction first prior to Carol and some others with Carol’s first. The reason is network traffic.
Here, as the account balance of Alice is 5 BTC, only one transaction either Bob’s or Carol’s is approved. Therefore, some will accept Bob’s transaction, marking Carol’s invalid. Same way, some accept Carol’s transaction, marking Bob’s invalid. The miners later create the block based on the transaction that is marked valid.
At the end of mining, the transaction which is included in the selected block will be approved by the network, and the other transaction will be rejected. Thus solving the double-spending issue.
What if two miners simultaneously find solution?
Imagine one block has Bob’s transaction and another Carol’s. At this point, both these blocks are considered valid. But only one can be added to the existing chain. So, what’s next ?
Though this is a rare scenario, Bitcoin has a solution to this problem. The blockchain will go for branching as the nodes have to consider both blocks for time being.
Now we have a “fork” in the network.
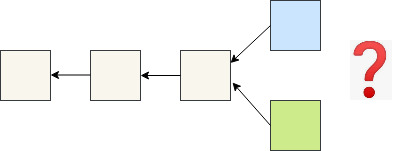
Now the question is which branch should be considered while mining the next block ? The selection is made based on the “longest chain rule”.
Dealing with Longest Chain Rule
PoW is computationally intensive and complex process. The block that required a higher amount of work, spending maximum hashing power, will represent the network majority under PoW. This block will be used as the parent block of the next block to be mined under fork discarding other branch (stale block).
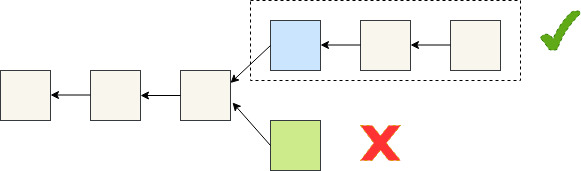
Selection Criteria
The length of a chain is measured by the amount of work done. The total amount of PoW spent to create a chain is calculated by adding the difficulty recorded in each block in that chain. Heavier the work, longer will be the chain. Therefore, fork resolution is based on the complexity of consensus algorithm. Forks can occur even without double spending, say if multiple miners manage to solve the puzzle and mine a block at the same time.
The forks which we have discussed so far are soft forks. It does not cause a permanent split in blockchain. There can be other scenarios in which forking occurs. It can be changes in the underlying software, certain upgrades for bug-fixing so on. These are known as hard forks as they are not backward compatible and will result in splitting the blockchain permanently. Miners who continue to run the old software, will see the new transactions invalid.
But this does not mean the double spending can be completely eliminated in a blockchain network. Let us see another scenario.
A malicious user, Mark tries to create a transaction which transfers 5 BTC to Charley to make a purchase. To avoid the service delay, Charley delivers the service without waiting for transaction confirmation.
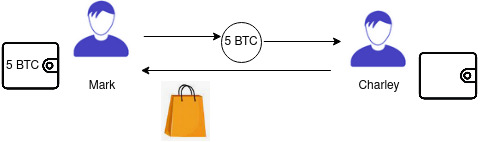
Meanwhile Mark initiates a self transaction that transfers the same 5 BTC to himself.
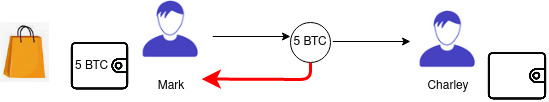
To record his transaction, Mark manages to influence 51% of the blockchain network and continue adding blocks to a chain much faster. This creates a longer chain to the chain that recorded Charley’s transaction. Thus the network has a fork. To resolve the fork, network choose the longest chain and invalidate the chain containing Charley’s transaction. This results Charley denying the payment and Mark succeeding the purchase without paying Charley.
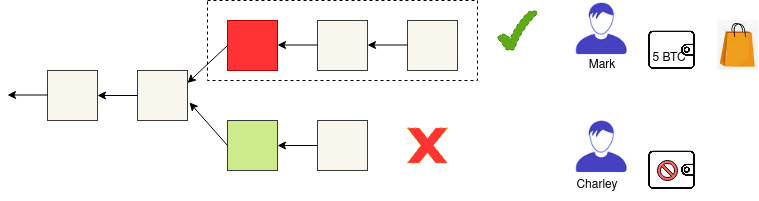
Here the attacker, Mark, takes advantage of a blockchain fork. A 51% attack allows an attacker to double-spend his own transactions in the longer chain, rejecting the transaction in the old chain.
This is moreover unlikely to happen as it requires a large amount of miners or a single miner with more that 50% of the network’s hash power. Expensive mining hardware and high energy consumption will be required to build a longer chain.
However, this situation could have been avoided if Charley waited for confirmations before providing the service. Bitcoin insists that transaction should be considered valid only after receiving 6 confirmations ( at least 6 blocks are added after the block containing the transaction).
To conclude, the double spending risk of cryptocurrency cannot be completely resolved. However, with the increasing number of participants and blocks in the chain, the chances for fake transactions getting included in the blockchain is unlikely or lesser in number.